Set Up Okta SSO
This article describes how to integrate Okta with Ataccama ONE Agentic Data Trust Platform using SAML 2.0 federation.
How sign-in works
When Okta SSO is configured, Ataccama acts as the SAML Service Provider (SP), and Okta acts as the Identity Provider (IdP). On sign-in, you are redirected to Okta for authentication (using your Okta credentials), and Okta returns a signed SAML assertion to Ataccama.
On first sign-in, Ataccama creates your user account automatically from the assertion attributes (email, first name, last name); on subsequent sign-ins, your profile attributes are refreshed from Okta.
|
Configure a separate identity provider for each Ataccama environment (for example, DEV, TEST, PROD). Each environment has its own realm and redirect URI, so the configuration cannot be shared across environments. |
Prerequisites
-
Okta admin access with permission to create SAML app integrations.
-
Environment admin access to the Ataccama Cloud Portal.
-
You have created the necessary Okta groups with the appropriate users assigned (only required if you want to use group-based role mapping in ONE).
Setup overview
Complete the following steps in order. Some values are generated in one step and reused in another, so keep both Okta and the Cloud Portal open throughout.
-
Get the redirect URI from Cloud Portal to use as the Single sign-on URL and Audience URI in Okta.
-
Configure SAML SSO in Okta: Create the app integration, define the SAML settings, attribute statements, and group attribute statement, and assign users.
-
Complete the Cloud Portal configuration: Enter the SAML metadata, map user attributes, and, optionally, import groups.
Get the redirect URI from Cloud Portal
-
In the Ataccama Cloud Portal, go to <your environment> > Settings.
-
Under Identity Provider (SSO), select Add.
-
In the Add Identity Provider dialog, switch to the SAML tab.
-
Note the Redirect URI shown. The URI is auto-generated for your environment realm and is read-only.
Example:
https://<your-domain>.ataccama.one/auth/realms/<tenant-name>/broker/saml/endpoint.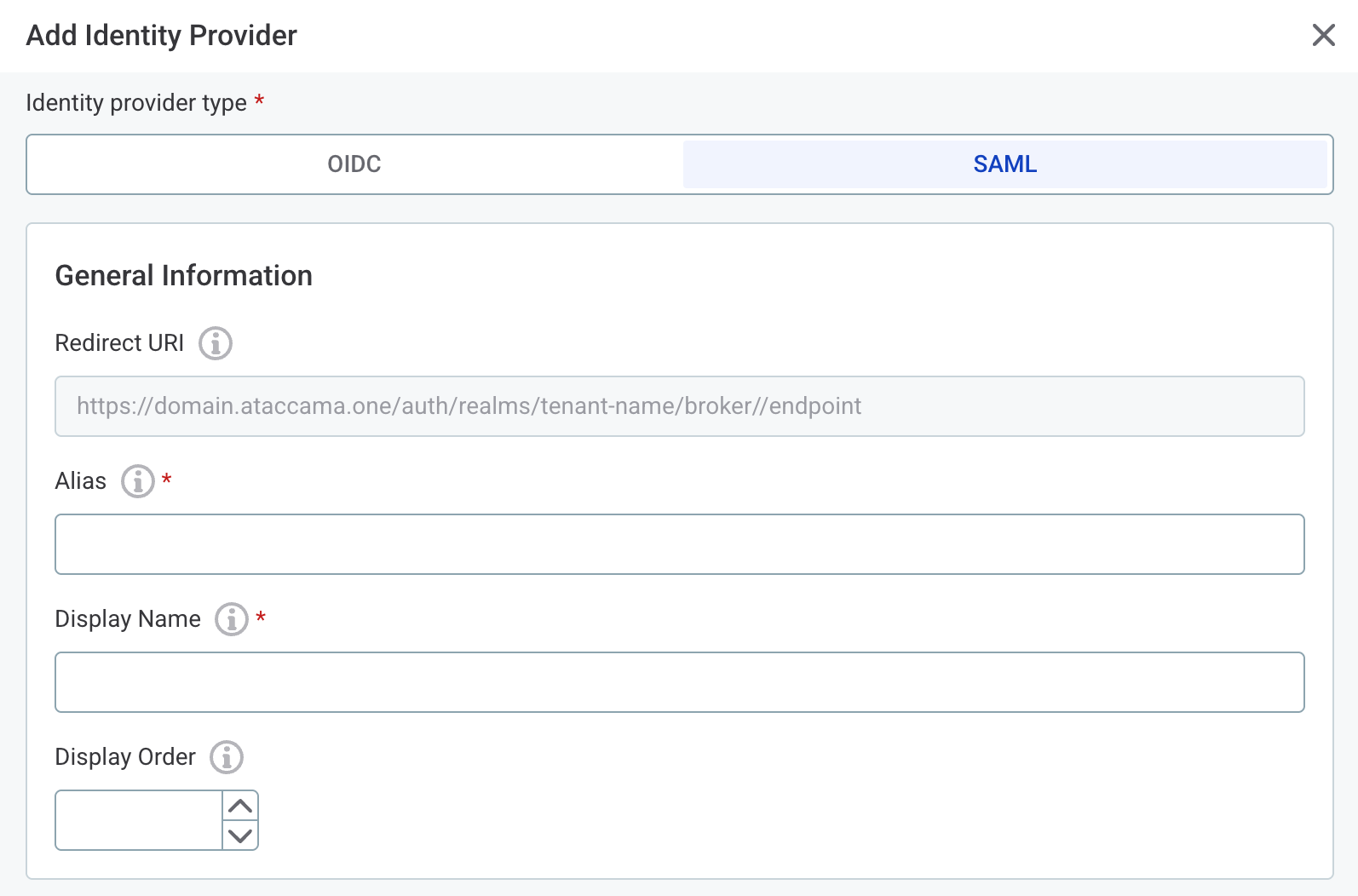
|
Keep this dialog open. You return to it in Complete the Cloud Portal configuration. |
Configure SAML SSO in Okta
Follow the Okta documentation to complete these steps:
-
Create a SAML app integration.
When prompted to choose a sign-in method, select SAML 2.0. Use
Ataccama ONEas the App name (or your preferred name).-
When configuring SAML settings, set the following:
-
Single sign-on URL: The redirect URI from Cloud Portal.
-
Audience URI (SP Entity ID): The redirect URI from Cloud Portal.
-
Name ID format:
EmailAddress. -
Application username:
Email.
-
-
Define attribute statements. The names you choose here must match the User attribute settings you enter in the Cloud Portal later.
-
firstName: Name formatBasic, valueuser.firstName. -
lastName: Name formatBasic, valueuser.lastName. -
email: Name formatBasic, valueuser.email.
-
-
Define group attribute statements if you want to use group-based role mapping in ONE. The attribute name you choose here must match the Mapping attribute name you enter in the Cloud Portal later.
-
Name:
groups(or your preferred name). -
Name format:
Basic. -
Filter: Choose a filter that limits which groups are sent (for example, Starts with
Ataccama-).We do not recommend sending all groups without a filter. SAML assertions have a size limit, and including hundreds of group entries can cause the sign-in to fail.
-
-
On the final step of the wizard, select I’m an Okta customer adding an internal app and This is an internal app that we have created, then Finish.
-
-
Assign the app integration to the users and groups that should have access to ONE.
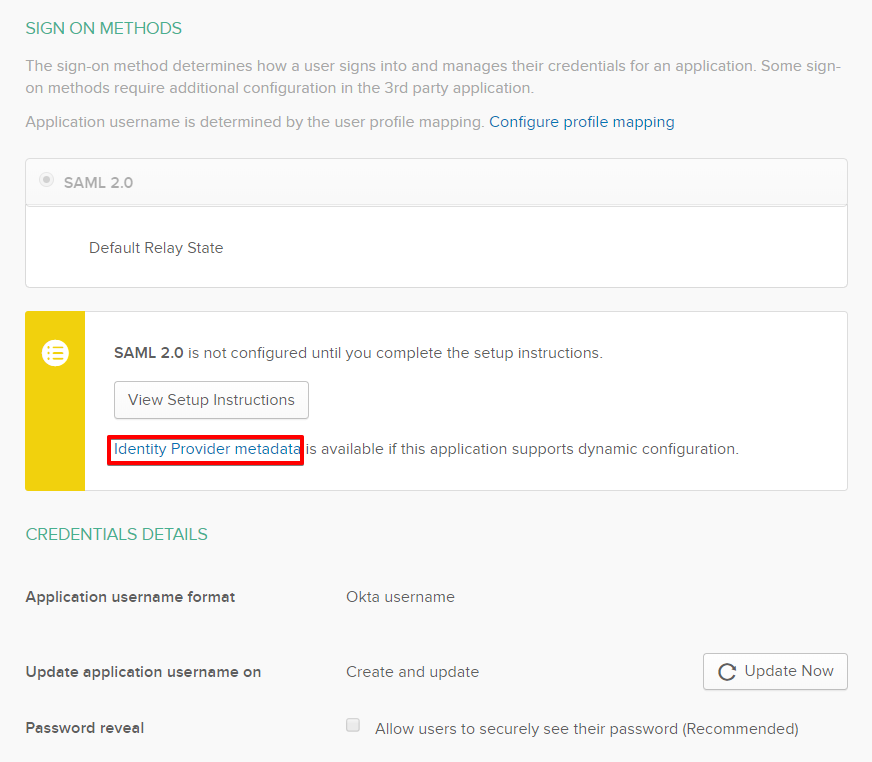
After you configure Okta, open the Sign On tab of your application and select View SAML setup instructions. Copy the metadata URL (recommended for autocompleting SAML settings) and complete the Cloud Portal configuration.
Alternatively, you can use the Identity Provider Single Sign-On URL and Identity Provider Issuer values, which have to be entered manually.
Complete the Cloud Portal configuration
Return to the Add Identity Provider dialog in the Cloud Portal and fill in the following.
General information
-
Alias: A short unique identifier. Leave the default (
saml) or enter your own (for example,okta-saml). -
Display Name: The label shown on the login screen (for example,
Okta). -
Display Order: Optional. Sets the order of this provider when multiple identity providers are configured.
SAML settings
-
Use discovery endpoint: Select this and paste the Okta metadata URL to automatically fill in the following fields.
-
Identity Provider Entity ID: The Identity Provider Issuer from Okta (for example,
http://www.okta.com/<okta-id>). -
Single Sign-On Service URL: The Identity Provider Single Sign-On URL from Okta.
-
Single Logout Service URL: Optional.
-
Name ID Policy Format:
Email. -
Want Assertions Signed: Enabled (recommended).
-
Validate Signature: Enabled (recommended).
You can leave all other SAML settings as default.
User attribute settings
Select Pre-fill for Okta to populate all four attribute fields with the default Okta values (and the Mapping attribute name in Group import (optional)). The pre-filled values are:
-
Username Attribute:
email -
Email Attribute:
email -
First Name Attribute:
firstName -
Last Name Attribute:
lastName
These values must exactly match the names you defined in Okta’s Attribute Statements (case sensitive).
Both Username Attribute and Email Attribute map to email because the Application username in Okta is set to Email.
Group import (optional)
To import Okta groups for role assignment in ONE:
-
Select Enable group mapping.
-
In Mapping attribute name, enter the name of the Group Attribute Statement you defined in Okta (for example,
groups; pre-filled if you used Pre-fill for Okta). -
Add one row per group:
-
Group name: The Okta group name, exactly as configured.
-
Description: An optional label visible only in ONE.
-
You can add or update groups at any point after the initial configuration.
Troubleshooting
Login fails after configuration
-
Verify that the Single sign-on URL and Audience URI in Okta exactly match the Redirect URI from the Cloud Portal.
-
Verify that the Entity ID and SSO URL in the Cloud Portal match the values from Okta’s View SAML setup instructions.
User profile attributes are missing or incorrect
-
Confirm that the attribute names in the Cloud Portal User attribute settings exactly match the names in Okta’s Attribute Statements (case sensitive).
-
Inspect the SAML assertion that Okta is sending (see Debug the SAML assertion).
Group memberships are not reflected
-
Verify that the Group Attribute Statement in Okta is configured and that the filter includes the expected groups.
-
Confirm that the Mapping attribute name in the Cloud Portal matches the name used in Okta’s Group Attribute Statement.
-
Verify that the user is a member of the relevant Okta groups and that those groups are assigned to the application.
Debug the SAML assertion
To inspect what Okta is actually sending:
-
Open an incognito browser window and go to Developer Tools > Network tab with Preserve log enabled.
-
Attempt to sign in using the SSO option.
-
Find the POST request that contains
SAMLResponse. -
Copy the value and decode it with a SAML decoder, for example, SAMLTool.
-
Verify that all expected attributes (
email,firstName,lastName, and the group attribute if configured) are present in<AttributeStatement>.
Was this page useful?
