MDM Web App Security Configuration
Authentication
Configure client URLs in Keycloak
Edit the following clients in Keycloak following the steps described in this section:
-
mdm-admin-client -
mdm-token-client-
Open the Keycloak administration console.
-
Make sure Ataccamaone realm is selected.
-
Select Clients.
-
From the list of clients, select the client identifier to open the configuration.
-
Depending on the client Access Type setting, different configuration fields are available and filled in.
Edit all filled-in fields that contain URLs, for example, Valid Redirect URIs, Base URL, and Admin URL.
Change the
http://localhost:<port>part to the actual client location. -
Select Save.
-
Repeat steps 3-7 for all relevant clients.
To change the default client password, switch to the Credentials tab of the client configuration and click Regenerate Secret. For basic authentication, enable Direct Access Grants Enabled option in the Keycloak client. 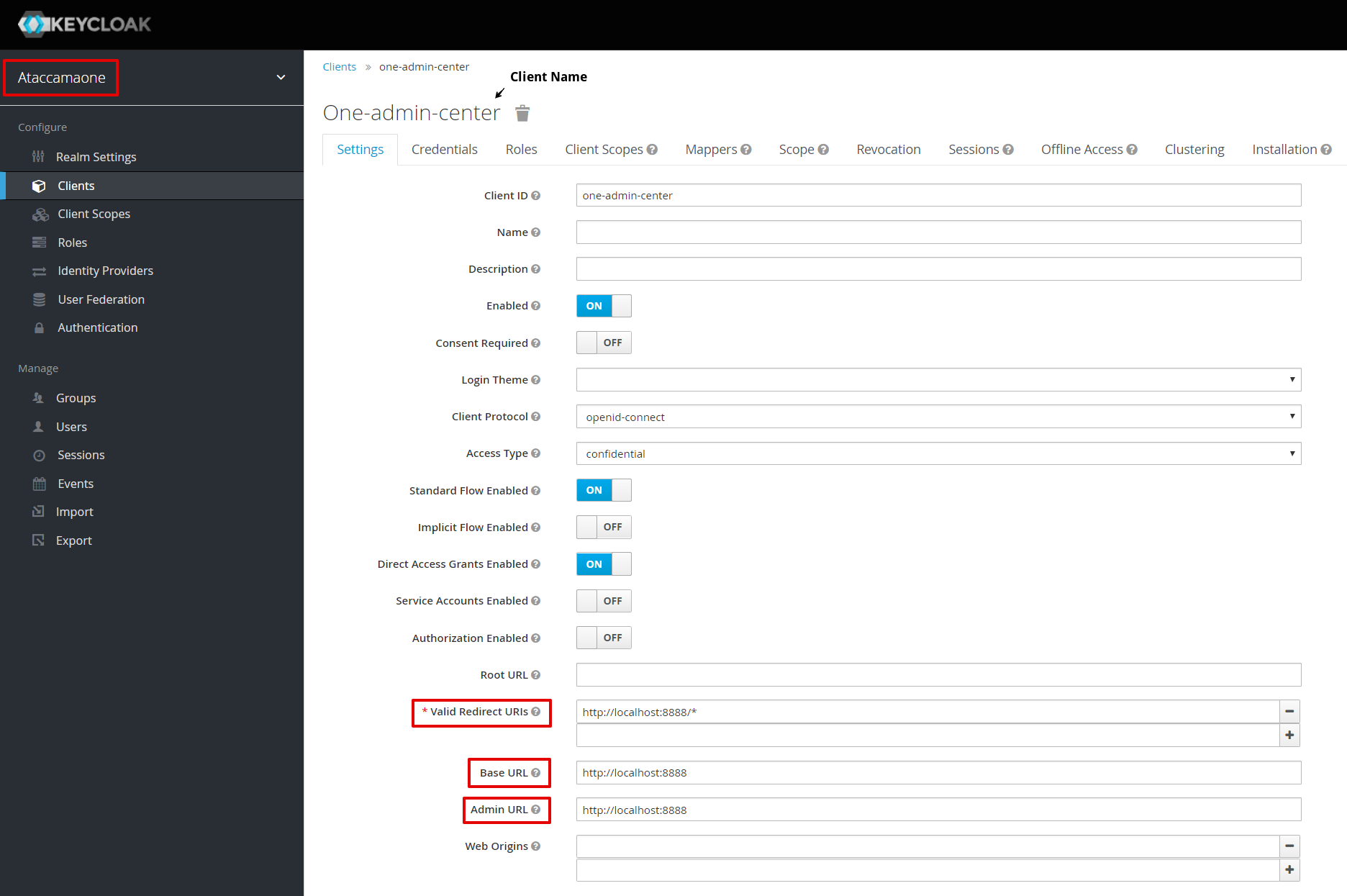
-
Edit client configuration files
To define the configuration for your Keycloak clients, add or edit the KeycloakDeploymentContributor element in the runtime configuration file.
The settings should correspond to the Keycloak settings for the clients.
| Keycloak is case-sensitive. Make sure to use lowercase if referring to the Keycloak server URL via hostname. |
The following is a sample KeycloakDeploymentContributor configuration for MDM Web App:
<config class="com.ataccama.server.keycloak.KeycloakDeploymentContributor">
<keycloakConfigs>
<keycloakConfig name="keycloak-local">
<url>http://localhost:8083/auth</url>
<realm>ataccamaone</realm>
<attributes>
<attribute name="ssl-required" value="external"/>
<attribute name="principal-attribute" value="preferred_username"/>
</attributes>
<clients>
<client id="mdm-admin-client">
<secret>mdm-admin-client-s3cret</secret>
</client>
<client id="mdm-token-client">
<secret>mdm-token-client-s3cret</secret>
<attributes>
<attribute name="use-resource-role-mappings" value="false"/>
<attribute name="public-client" value="false"/>
<attribute name="bearer-only" value="false"/>
<attribute name="autodetect-bearer-only" value="false"/>
<attribute name="always-refresh-token" value="false"/>
<attribute name="enable-basic-auth" value="true"/>
</attributes>
</client>
</clients>
</keycloakConfig>
</keycloakConfigs>
</config>Edit the following client adapter files so that MDM Web App connects to Keycloak properly:
-
On the web application server, edit
mdm/etc/application.properties.ataccama.authentication.keycloak.realm=ataccamaone ataccama.authentication.keycloak.server-url=http://localhost:8083/auth ataccama.authentication.keycloak.token.client-id=mdm-webapp-public-client # Keycloak public client ID for web application browsing ataccama.authentication.keycloak.public.client-id=$\{ataccama.authentication.keycloak.token.client-id} ataccama.authentication.keycloak.token.secret=mdm-webapp-public-client-s3cret ataccama.authentication.keycloak.token.issuer=$\{ataccama.authentication.keycloak.server-url}/realms/$\{ataccama.authentication.keycloak.realm}For information about how to encrypt passwords, see Encrypting Passwords. -
In the project configuration
Files/etc/issue_management/directory, edit the DQITconfig.xmlfile.
In most cases, it is only necessary to modify the ataccama.authentication.keycloak.server-url attribute, which corresponds to the base URL of the Keycloak server.
Treat other settings as expert and modify only if you know what you are doing.
| Keycloak is case-sensitive. Make sure to use lowercase if referring to the Keycloak server URL via hostname. |
Check Http Dispatcher Configuration
In the Server Configuration file, check that all intercept URLs and deployment contexts appear as shown below.
The default server configuration file mdm.serverConfig for MDM Engine is located in Files > etc project folder.
<component disabled="false" class="com.ataccama.dqc.web.HttpDispatcher">
<filters/>
<listeners>
<listenerBean healthstateRefreshRate="60000" maxWaitingRequests="10" backlog="50" waitingRequestsWarningThreshold="1" port="8051" threadPoolTimeout="10000" healthStateRecoveryTimeout="300000" name="default" threads="50" servletOnly="false" ssl="false">
<contexts>
<listenerContext path="/" htmlErrorPages="false">
<filterChains>
<filterChain path="/*" filters="securityFilter">
<conditions/>
</filterChain>
</filterChains>
<securityFilter loginUrl="/sso/login" class="com.ataccama.server.http.security.keycloak.KeycloakSecurity">
<identityProviders>
<identityProvider configName="keycloak-local" clientId="mdm-token-client" pattern="/api/mda/**"/>
<identityProvider configName="keycloak-local" clientId="mdm-token-client" pattern="/api/export/mda/**"/>
<identityProvider configName="keycloak-local" clientId="mdm-token-client" pattern="/api/userSettings/**"/>
<identityProvider configName="keycloak-local" clientId="mdm-token-client" pattern="/api/issueTrackerMda/**"/>
<identityProvider configName="keycloak-local" clientId="mdm-token-client" pattern="/api/dqit/**"/>
<identityProvider configName="keycloak-local" clientId="mdm-token-client" pattern="/api/graphql/mda/**"/>
<identityProvider configName="keycloak-local" clientId="mdm-token-client" pattern="/dqitIssueEvent"/>
<identityProvider configName="keycloak-local" clientId="mdm-token-client" pattern="/soapOverHttp/**"/>
<identityProvider configName="keycloak-local" clientId="mdm-token-client" pattern="/nme-rest/**"/>
<identityProvider configName="keycloak-local" clientId="mdm-token-client" pattern="/**"/>
</identityProviders>
<interceptUrls>
<interceptUrl access="permitAll" pattern="/xmlRpcOverHttp/**"/>
<interceptUrl access="permitAll" pattern="/soapOverHttp/**"/>
<interceptUrl access="permitAll" pattern="/soapServices/**"/>
<interceptUrl access="isAuthenticated()" pattern="/api/export/mda"/>
<interceptUrl access="isAuthenticated()" pattern="/**"/>
</interceptUrls>
</securityFilter>
</listenerContext>
</contexts>
</listenerBean>
</listeners>
<servletFilters/>
</component>Web application security
You can configure MDM Web App security by adding response headers (security headers) to HTTP responses from the web application.
| We recommend setting security headers in case your web application is exposed to potential security attacks. |
The security headers are configured in the application.properties file.
They are commented out by default: uncomment them to enable.
| Name | Default value |
|---|---|
|
'self' ${ataccama.authentication.keycloak.server-url} |
|
* 'unsafe-inline' 'unsafe-eval' |
|
'self' data: |
Was this page useful?
